Clase 406 Luis Fernando Peña: Protecting Your Business From Digital Disasters
Have you ever stopped to think about what keeps a business running smoothly behind the scenes? It's not just about the products or services; it's also about the unseen digital backbone. Losing that crucial foundation, you know, can bring everything to a grinding halt. We're talking about something as vital as Active Directory, which, honestly, is the heart of identity services for many organizations. When it falters, everything can feel a bit chaotic, and that's where the insights from someone like Luis Fernando Peña, perhaps connected to something like "Clase 406," become incredibly important.
Many businesses, you see, simply cannot operate without Active Directory up and running. It’s the central hub for user authentication, network resources, and so much more. Imagine a world where employees cannot log in, access files, or even connect to their email. That, my friend, is a very real and pretty scary scenario. So, learning how to develop a comprehensive Active Directory disaster recovery strategy is, like, super important for anyone in charge of keeping things online.
This article explores the deep importance of having a solid plan for Active Directory recovery. We'll touch on key considerations, the tricky challenges that can pop up, and some practical steps for making sure your systems stay online, even when things go sideways. It's about being ready, really, for anything the digital world might throw your way, and understanding how a focus like "Clase 406 Luis Fernando Peña" could be all about preparing for these very moments.
- Malachy Murphy
- Heather Sylvia Adams
- Does Robert Duvall Have Any Children
- Tracey Cherelle Jones Dashiki
- Jann Mardenborough Audrey
Table of Contents
- Luis Fernando Peña: A Look at the Expert Behind the Class
- The Absolute Need for Active Directory Disaster Recovery
- What is Active Directory, Anyway?
- The Changing Face of Digital Threats
- Crafting Your Own Recovery Roadmap
- Key Things to Keep in Mind for AD Recovery
- Understanding "Clase": A Brief Linguistic Interlude
- Common Questions About Active Directory Recovery
- Wrapping Things Up: Your Next Steps
Luis Fernando Peña: A Look at the Expert Behind the Class
When we hear "Clase 406 Luis Fernando Peña," it naturally brings to mind someone with a lot of knowledge, perhaps a teacher or a thought leader. While we might not have all the specific details about this particular class or Luis Fernando Peña's exact role in it, we can imagine him as a guiding light in the complex area of IT resilience. He likely shares practical wisdom, helping others get ready for the unexpected. His work, you know, would probably focus on making sure businesses can keep going, no matter what digital challenges come their way.
Given the importance of Active Directory to so many organizations, it’s quite possible that a "Clase 406" led by Luis Fernando Peña might focus heavily on IT disaster preparedness, with a special emphasis on identity services. He could be someone who has seen it all, someone who understands the ins and outs of keeping critical systems safe. That kind of experience is, honestly, invaluable.
Here’s a quick look at what we might expect from a profile of someone like Luis Fernando Peña, based on the kind of expertise needed for such a vital subject:
- New Teenxy
- Senpai Stream
- Characters In Shatter Me
- Jennifer Rauchet
- Jackerman Mother Warmth Chapter 3 Release Date
| Detail | Description |
|---|---|
| Name | Luis Fernando Peña |
| Known For | Expertise in Active Directory Disaster Recovery, Business Continuity Planning, Cybersecurity Education |
| Possible Affiliation | Instructor for "Clase 406" (focused on IT resilience), IT Consultant, Author |
| Key Focus Areas | Proactive AD Recovery, Ransomware Mitigation, Cloud Identity Integration (e.g., Entra ID), Incident Response |
| Philosophy | Emphasizes preparation, rigorous testing, and practical, adaptable recovery strategies. |
His insights would surely help bridge the gap between theoretical knowledge and real-world application, which is so, so important for anyone looking to truly protect their digital assets. It's almost like having a roadmap from someone who's already traveled the difficult terrain.
The Absolute Need for Active Directory Disaster Recovery
Active Directory disaster recovery has, you know, always been an extremely complicated process. It usually requires lengthy preparation, careful planning, and a lot of testing. This isn't just a casual task; it's a critical part of making sure a business can keep its doors open, digitally speaking. Without a solid plan, a company could face significant loss of production and frustrating downtime, which nobody wants.
Think about it: Active Directory is basically the central brain for Windows domains. It manages user accounts, computer settings, and access permissions. If that brain stops working, everything connected to it grinds to a halt. A perfect Active Directory disaster recovery service, then, can really prevent important and confidential information from being lost due to unexpected disasters. It's pretty much your digital safety net, honestly.
To mitigate these serious risks, it’s absolutely essential to establish a very robust disaster recovery plan for Active Directory. This isn't just a nice-to-have; it's a must-have. We'll explore some best practices for AD disaster recovery, emphasizing the importance of proper documentation, thorough testing, and, you know, considering all sorts of different disaster scenarios. It's about being prepared for anything, really.
What is Active Directory, Anyway?
So, what exactly is Active Directory? At its core, it's a directory service developed by Microsoft for Windows domain networks. It's where all the information about users, computers, and other network resources is stored. When you log into your computer at work, Active Directory is what checks your username and password. It also dictates what files you can access and what applications you can use. It's pretty much the gatekeeper and the organizer of your entire network environment.
Because it handles all these critical identity services, Active Directory is, you know, absolutely central to how a business operates. If it goes down, employees can't log in, servers can't communicate properly, and applications stop working. This means business operations can just stop completely. That's why protecting it and having a way to bring it back quickly is so, so important.
The continuity of identity services during failures, cyberattacks, or unforeseen disasters really depends on a well-thought-out plan for Active Directory and Entra ID (which was formerly Azure AD). It’s not just about getting things back online; it’s about getting them back online fast and without losing precious data. This is where the kind of insights you'd get from a "Clase 406" become invaluable, as they'd likely break down these very concepts.
The Changing Face of Digital Threats
In the past, recovering Active Directory from scratch was, honestly, quite uncommon. Disasters happened, sure, but the nature of the threats was a bit different. However, due to the very significant increase in ransomware attacks and other sophisticated threats that have appeared in recent years, the possibility of losing your Active Directory has become a much more real and pressing concern. This shift in the threat landscape is something every organization needs to acknowledge.
Ransomware, for instance, can encrypt your entire network, including your Active Directory servers, making them completely unusable. Other cyberattacks might corrupt data or introduce malicious code that compromises the integrity of your identity services. This means that a disaster recovery plan isn't just for natural disasters or hardware failures anymore; it's also, you know, a vital defense against malicious actors.
This changing environment makes proactive Active Directory disaster recovery best practices more important than ever. It's not enough to just back up your data; you need a strategy that considers how to recover from these new, more aggressive types of attacks. It's a bit like updating your home security system for a new kind of threat; you need to adapt. Luis Fernando Peña, in a class like "Clase 406," would surely highlight these modern challenges.
Crafting Your Own Recovery Roadmap
Given that this guide serves only as a template for forest recovery, it's absolutely vital that you devise a custom forest recovery plan that suits your specific environment and meets your business needs. No two businesses are exactly alike, so a one-size-fits-all approach simply won't cut it. This customization is, like, super important for a successful recovery.
Depending on your environment and business requirements, you may not need to perform all the steps described in a comprehensive guide to perform a successful forest recovery. Some steps might be more relevant to very large, complex setups, while others are universally applicable. It's about picking and choosing what makes sense for you, you know, and building a plan that's truly effective.
This whole process requires careful consideration of your unique infrastructure, your recovery time objectives (how quickly you need to be back online), and your recovery point objectives (how much data loss you can tolerate). It's a strategic exercise, really, that goes beyond just technical steps. It's about aligning your IT resilience with your business goals, which is a big deal.
Document Everything (And Then Some)
Proper documentation is, honestly, the bedrock of any good disaster recovery plan. This means not just documenting your Active Directory configuration, but also your recovery procedures, contact lists, and any dependencies. Think of it as a detailed instruction manual for getting your business back on its feet. Without it, you're essentially trying to rebuild a complex system from memory, which is, you know, pretty difficult.
Your documentation should be clear, concise, and accessible, even during a crisis. It should outline every step, from identifying the disaster to restoring services. It's not just for the IT team; it should be understandable enough for others to follow, perhaps with some guidance. This level of detail is, like, absolutely critical when time is of the essence.
Remember to keep your documentation updated regularly. As your environment changes, so too should your recovery plan and its associated documents. An outdated plan is, in a way, almost as bad as no plan at all. This ongoing effort is a very small price to pay for peace of mind, really.
Practice Makes Perfect: Testing Your Plan
A disaster recovery plan, no matter how well-written, is basically useless if it hasn't been tested. Testing allows you to identify weaknesses, refine procedures, and ensure that everyone involved knows their role. It’s not just about checking boxes; it’s about building confidence and muscle memory within your team. You know, it's like a fire drill for your IT systems.
You should test your Active Directory disaster recovery plan regularly, perhaps annually or whenever there are significant changes to your environment. These tests can range from tabletop exercises, where you walk through the steps mentally, to full-blown simulations, where you actually attempt to restore a test environment. The more realistic the test, the better prepared you'll be, obviously.
During testing, pay close attention to the timing of each step and any unexpected challenges that arise. These insights are incredibly valuable for refining your plan and making it more efficient. It's about learning and adapting, you know, before a real disaster forces you to. Luis Fernando Peña would, I imagine, emphasize this point strongly in "Clase 406," because practical experience is so important.
Thinking About All the "What Ifs"
When you're planning for disaster recovery, it's really important to consider various disaster scenarios. This means thinking beyond just a server crash. What if there's a major power outage? What if a cyberattack completely wipes out your data? What if a natural disaster affects your primary data center? Each scenario might require a slightly different approach, honestly.
Consider scenarios like a full Active Directory forest corruption, a domain controller compromise, or even the accidental deletion of critical objects. For each scenario, outline the specific steps required for recovery. This level of detail ensures that your team isn't caught off guard, you know, no matter what happens. It's about having a playbook for every possible bad day.
Also, think about the dependencies. Does your Active Directory rely on DNS? What about other applications? A comprehensive plan considers the entire ecosystem, not just isolated components. This holistic view is, like, absolutely essential for a truly effective recovery strategy. It's a bit like mapping out all the connections in a very complex puzzle.
Key Things to Keep in Mind for AD Recovery
The following are extremely useful resources for understanding Active Directory backup and disaster recovery. While I can't link to specific external resources here, you should look for official documentation on known issues for AD DS backup and recovery, and best practices for AD DS backup and recovery. These resources are, you know, absolutely invaluable for deep technical insights.
Microsoft Active Directory disaster recovery plan is, honestly, an essential part of domain management. To avoid loss of production and downtime, it is the very best solution. It's about being proactive rather than reactive. This planning helps you maintain business continuity, which is, after all, the main goal.
Some tips that can help with proactive Active Directory disaster recovery include: regularly backing up your system state, testing those backups, having an offsite storage strategy, and understanding the different recovery modes for Active Directory. These steps, you know, form the backbone of a solid defense against data loss and system failure.
For instance, implementing a disaster recovery solution for Active Directory and DNS with cloud services like Azure Site Recovery can provide a powerful safety net. This allows you to replicate your Active Directory environment to a secondary location, ready to fail over if your primary site goes down. It's a very modern approach to an age-old problem, honestly.
You can learn more about Active Directory disaster recovery on our site, which offers a broader look at strategies and tools. Also, this page explores specific challenges in identity management during unforeseen events. These resources, you know, can help you deepen your knowledge and refine your own plans.
Understanding "Clase": A Brief Linguistic Interlude
It's interesting how the word "clase" itself carries so much meaning, especially when we talk about "Clase 406 Luis Fernando Peña." In Spanish, "clase" translates to "class" in English. This could mean a school class, a type of thing, or even social standing. Normally, I can tell when a noun is masculine or feminine, but the word "clase" for "class" is a bit tricky, honestly.
For example, if I need to say the sentence "the algebra class," it's translated as "la clase de álgebra." This indicates that "clase" is feminine. See, "la" is the feminine definite article. It's a bit of a linguistic quirk, but it's important for proper Spanish grammar, you know, to get these details right. This small linguistic point highlights how specific terms can have deep implications, even in technical fields.
There's also a difference between "clase" and "lección." "Clase" refers to the entire teaching session or the group of students, while "lección" usually means a specific lesson or a single teaching point within a class. So, "Clase 406" would refer to the entire course or group of students, not just one lesson. It's a small but significant distinction, you know, when you're talking about educational settings.
You might also hear "salón de clase" for classroom, or "el aula." One of my workbooks uses "la sala de clase" for classroom, and some learning tools use "el aula." When I looked up "classroom" in a dictionary, it didn't make any distinction between the two, so I was wondering if one or the other is more commonly used and, more importantly, where. It's pretty much a regional thing, honestly, but both are understood. This bit of linguistic exploration, you know, just adds a little extra flavor to our discussion about "Clase 406."
Common Questions About Active Directory Recovery
People often have questions about how to best prepare for Active Directory recovery. Here are a few common ones, you know, that come up quite a bit:
What's the most important step in Active Directory disaster recovery?
The most important step is, honestly, having a well-documented and regularly tested plan. Without a clear roadmap and practice, even the best tools won't help you much during a real crisis. It's about preparation, really, more than anything else.
How often should I test my Active Directory recovery plan?
You should test your plan at least annually, or whenever there are significant changes to your IT environment, like major upgrades or new applications. More frequent testing, you know, is always better if your resources allow it. It helps keep everyone sharp and ready.
Can cloud services help with Active Directory disaster recovery?
Absolutely, yes. Cloud services like Azure Site Recovery can provide powerful replication and recovery capabilities for your Active Directory. They offer offsite recovery options and can significantly reduce your recovery time objectives. It's a very modern and effective approach, honestly, for business continuity.
Wrapping Things Up: Your Next Steps
Protecting your Active Directory is, you know, not just an IT task; it's a fundamental business imperative. As we've seen, the insights you might gain from someone like Luis Fernando Peña, perhaps through a "Clase 406," can be absolutely vital for developing a strong defense against digital disruptions. It's about understanding the complexities and putting practical strategies into action.
Your journey towards a truly resilient Active Directory environment starts with acknowledging the critical role it plays in your operations. Then, it moves to careful planning, thorough documentation, and rigorous testing. Remember, the digital landscape is always changing, so your recovery plan should be a living document, constantly updated and refined. This proactive approach is, honestly, your best bet for avoiding significant downtime and data loss. So, take the time to build that strong foundation.
- Leafyishere
- Cassie Ventura Nude
- Tjr Trades Roleplayed His Entire Career
- Emily Rudd Nude
- Kylan Darnell Parents Net Worth

20+ Personajes de Clase 406 y cómo han cambiado los actores que les
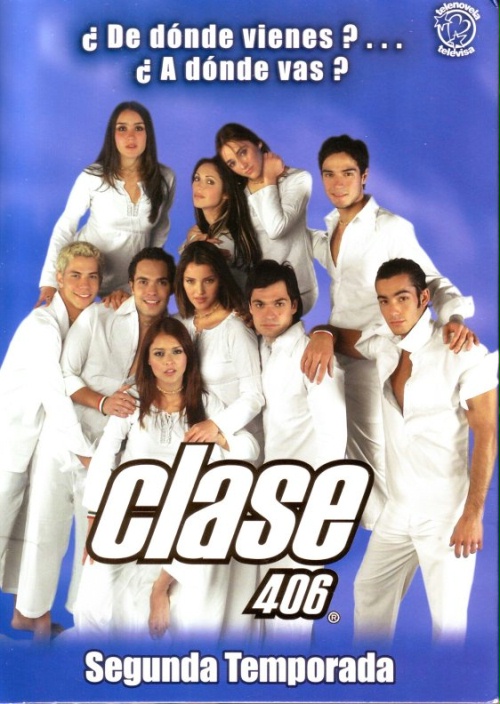
Clase 406 - Dulce María Wiki

Clase 406